相關新聞
BitRAT malware campaign uses stolen bank data for phishing
Threat actors behind a recent malware campaign have been using the stolen information of bank customers in Colombia as lures in phishing emails designed to infect targets with the BitRAT remote access trojan, according to cloud security firm Qualys. [...]
Bleepingcomputer
2023年01月04日 277 觀看次數
Over 60,000 Exchange servers vulnerable to ProxyNotShell attacks
More than 60,000 Microsoft Exchange servers exposed online are yet to be patched against the CVE-2022-41082 remote code execution (RCE) vulnerability, one of the two security flaws targeted by ProxyNotShell exploits. [...]
Bleepingcomputer
2023年01月04日 270 觀看次數

Synology fixes maximum severity vulnerability in VPN routers
Taiwan-based NAS maker Synology has addressed a maximum (10/10) severity vulnerability affecting routers configured to run as VPN servers. [...]
Bleepingcomputer
2023年01月03日 276 觀看次數
Extracting Encrypted Credentials From Common Tools
Attackers are harvesting credentials from compromised systems. Here's how some commonly used tools can enable this.
Dark Reading
2022年12月30日 284 觀看次數

What is a Gmail app password and how do you create one?
If third-party apps need to connect to your Gmail account, your regular Google account password may not be enough. Find out how to use the App Passwords feature and why.
ZDnet
2022年12月30日 1057 觀看次數

Hackers abuse Google Ads to spread malware in legit software
Malware operators have been increasingly abusing the Google Ads platform to spread malware to unsuspecting users searching for popular software products.
Bleepingcomputer
2022年12月29日 236 觀看次數

Thousands of Citrix Servers Still Unpatched for Critical Vulnerabilities
Thousands of Citrix Application Delivery Controller (ADC) and Gateway endpoints remain vulnerable to two critical security flaws disclosed by the company over the last few months. The issues in question are CVE-2022-27510 and CVE-2022-27518 (CVSS...
The Hacker News
2022年12月29日 424 觀看次數

BlueNoroff APT Hackers Using New Ways to Bypass Windows MotW Protection
BlueNoroff, a subcluster of the notorious Lazarus Group, has been observed adopting new techniques into its playbook that enable it to bypass Windows Mark of the Web (MotW) protections. This includes the use of optical disk image (.ISO extension) and virtual hard disk...
The Hacker News
2022年12月27日 317 觀看次數

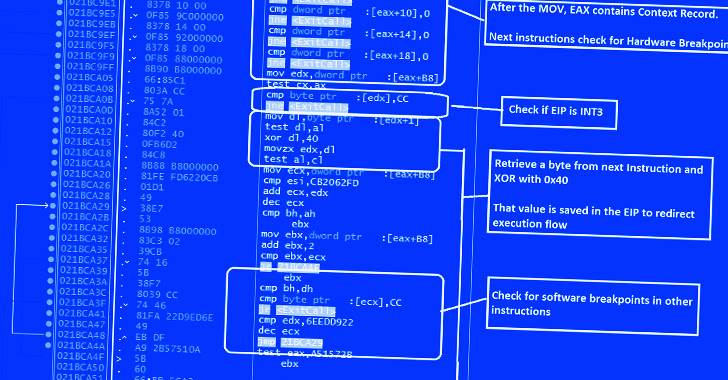
GuLoader Malware Utilizing New Techniques to Evade Security Software
Cybersecurity researchers have exposed a wide variety of techniques adopted by an advanced malware downloader called GuLoader to evade security software. "New shellcode anti-analysis technique attempts to thwart researchers and hostile environments by scanning entire process memory for any virtual machine (VM)-related...
The Hacker News
2022年12月26日 292 觀看次數
Back to work, Linux admins: You have a CVSS 10 kernel bug to address
Also, script kiddies are coming for your gift cards, and Meta's Cambridge Analytica pathetic payout
Merry Christmas, Linux systems administrators: Here's a kernel vulnerability with a CVSS score of 10 in your SMB server for the holiday season giving an unauthenticated...
The Register
2022年12月24日 321 觀看次數

