Oracle Java Flaws Let Remote Execute Arbitrary Code Vulnerabilities
Last Update Date:
3 Feb 2013
Release Date:
21 Jan 2013
5162
Views
RISK: High Risk
TYPE: Clients - Productivity Products

Multiple vulnerabilities have been identified in Oracle Java. which can be exploited by remote user to compromise a user's system.
A remote user can create specially crafted Java content that, when loaded by the target user, will execute arbitrary code on the target user's system. The code will run with the privileges of the target user
On version Java 7 Update 11, user confirmation is required in order for unsigned or self-signed Java applets to run.
Impact
- Remote Code Execution
System / Technologies affected
- Oracle Java 7 Update 11 and prior versions
Solutions
Before installation of the software, please visit the software manufacturer web-site for more details.
- Apply Oracle Java SE Critical Patch Update - Feb 2013 :
http://www.oracle.com/technetwork/topics/security/javacpufeb2013-1841061.html- Update to Java SE JDK/JRE Version 7 Update 13, JDK/JRE Version 6 Update 39
http://www.java.com/en/download/
http://www.oracle.com/technetwork/java/javase/downloads/index.html
- Update to Java SE JDK/JRE Version 7 Update 13, JDK/JRE Version 6 Update 39
Workaround:
- Java 7 update 10 or later: Disable Java in web browsers.
http://www.java.com/en/download/help/disable_browser.xml
It is recommended to have the latest version of Java installed .
http://java.com/en/download/faq/remove_olderversions.xml - Prior to Java 7 update 10: If you are using Internet Explorer with older versions of Java, you can disable Java by following steps
1. In the Windows Control panel, change the View setting to "Classic View" in (Windows XP and Windows Vista) Or "Large icons" in (Windows 7) .
2. Open the Java item, select the "Advanced" tab. On "Default Java for Browser", click "+" to expand the options。
3. Select "Microsoft Internet Explorer", and then press the "Space" in keyboard to uncheck the selection.
For other browsers and OS, please refer to the following URL:
/my_url/en/blog/12082902#howtoprotect
- Once you have Java disabled, you may restart the browsers and verify if Java is not detected via the following link.
http://java.com/en/download/installed.jsp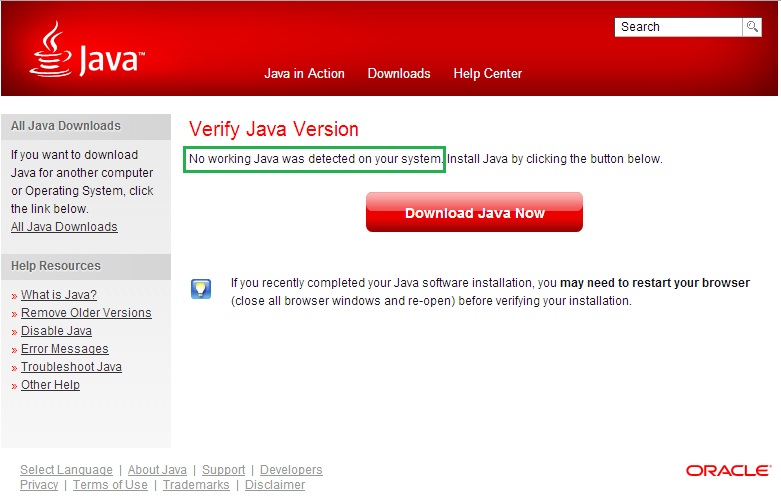
- Only enable Java temporarily in trusted sites (e.g. government and banks) when necessary. Do not browse any other websites when Java is enabled, disable it immediately after use.
- As a best practice of security, you should not install any software that you do not require. If you are not sure if you need Java, you can follow the steps in the workaround section to disable Java for some time to verify before you uninstall Java.
Vulnerability Identifier
- No CVE information is available
Source
Related Link
Share with
