Researchers said they recently discovered a zero-day vulnerability in the 7-Zip archiving utility that was actively exploited as part of Russia's ongoing invasion of Ukraine.
The vulnerability allowed a Russian cybercrime group to override a Windows protection designed to limit the execution of files downloaded from the Internet. The defense is commonly known as MotW, short for Mark of the Web. It works by placing a “Zone.Identifier” tag on all files downloaded from the Internet or from a networked share. This tag, a type of NTFS Alternate Data Stream and in the form of a ZoneID=3, subjects the file to additional scrutiny from Windows Defender SmartScreen and restrictions on how or when it can be executed.
There’s an archive in my archive
The 7-Zip vulnerability allowed the Russian cybercrime group to bypass those protections. Exploits worked by embedding an executable file within an archive and then embedding the archive into another archive. While the outer archive carried the MotW tag, the inner one did not. The vulnerability, tracked as CVE-2025-0411, was fixed with the release of version 24.09 in late November.
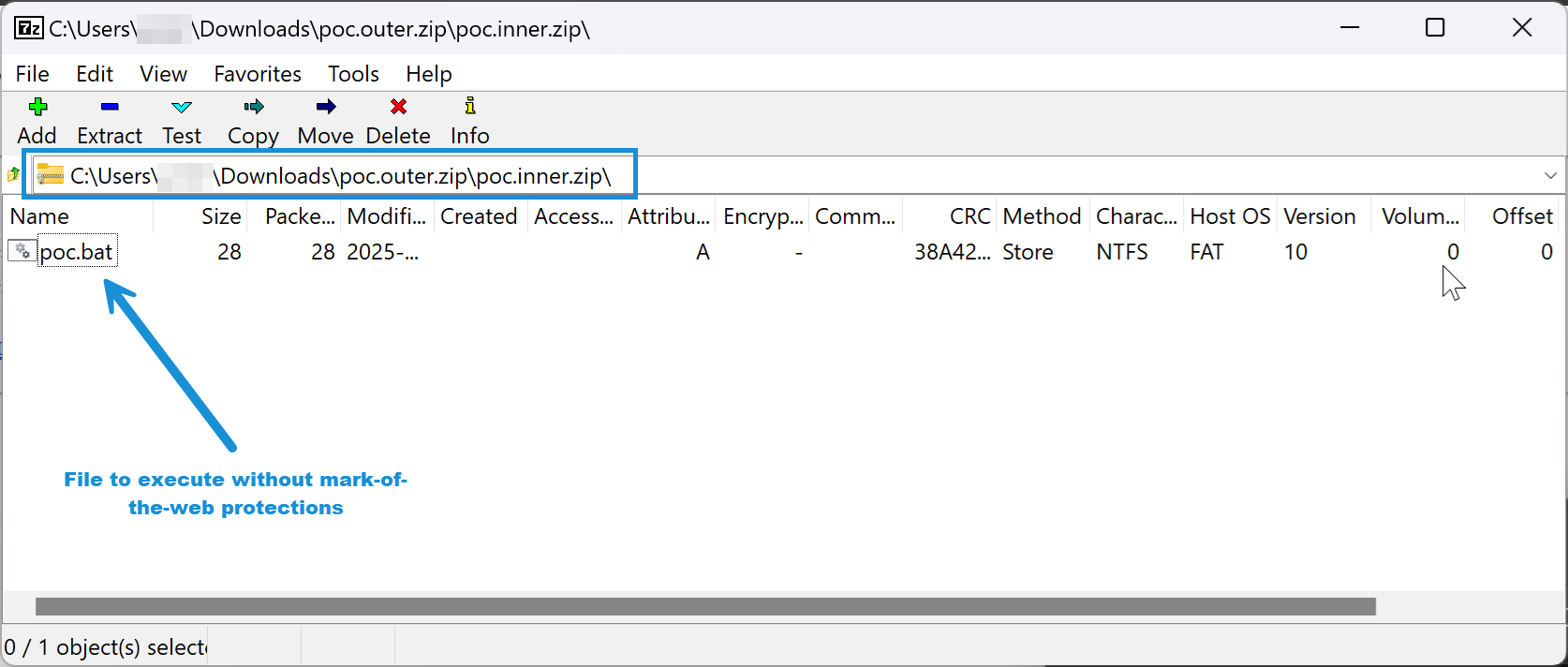
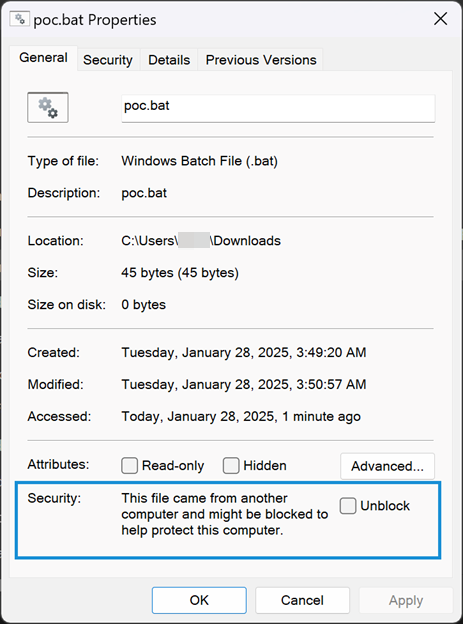
“The root cause of CVE-2025-0411 is that prior to version 24.09, 7-Zip did not properly propagate MoTW protections to the content of double-encapsulated archives,” wrote Peter Girnus, a researcher at Trend Micro, the security firm that discovered the vulnerability. “This allows threat actors to craft archives containing malicious scripts or executables that will not receive MoTW protections, leaving Windows users vulnerable to attacks.”




Windows commonly hides file extensions, so you can have a .pdf.exe that will show as being a .pdf. With a properly set file icon, it’ll look like a PDF but actually launch the executable.
However, the actual attack chain here is a little more clever than that, as detailed by the Trend Micro writeup (original file names are paraphrased in brackets):
1. {Documents and Payments}.7z is the outer 7z archive, which gets the MoTW flag and contains:
2. {List}.doc (with the c being a Cyrillic character) is an inner 7z archive to which the MoTW flag does not propagate. It in turn holds:
3. {Payment Order and Attachments}.url, which gets auto-opened thanks to the lack of MoTW (other files that can be auto-opened are .js (JavaScript) and .wsf (Windows Script File)). This file then reaches out to an attacker-controlled server to pull down:
4. invoce.zip, which has now avoided MoTW flagging entirely and contains:
5. {Payment Order}.pdf.exe, the actual malware payload.
Note that there are several points at which a user could go, “hmm, this is weird; I’m going to stop clicking on these files,” but all the files upon which the user clicks do look legitimate (besides the final one, whose .exe extension may or may not be hidden based on Windows settings).